Bytes.co News
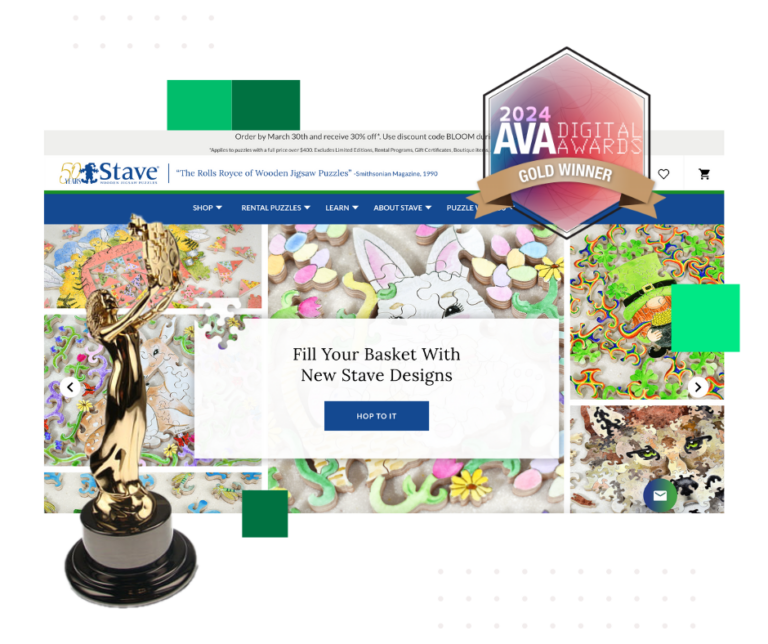
Bytes.co Wins 2024 AVA Digital Award for Outstanding SEO Work
Trust Company of Vermont Website Launch

Bytes.co Wins Third Consecutive Best Places to Work in Vermont Award
Unveiling Our Paw-some Creation: Animal Welfare Society Website Launch

A New Chapter at 7 Kilburn St. in Burlington, Vermont

2023: Our Year in Review
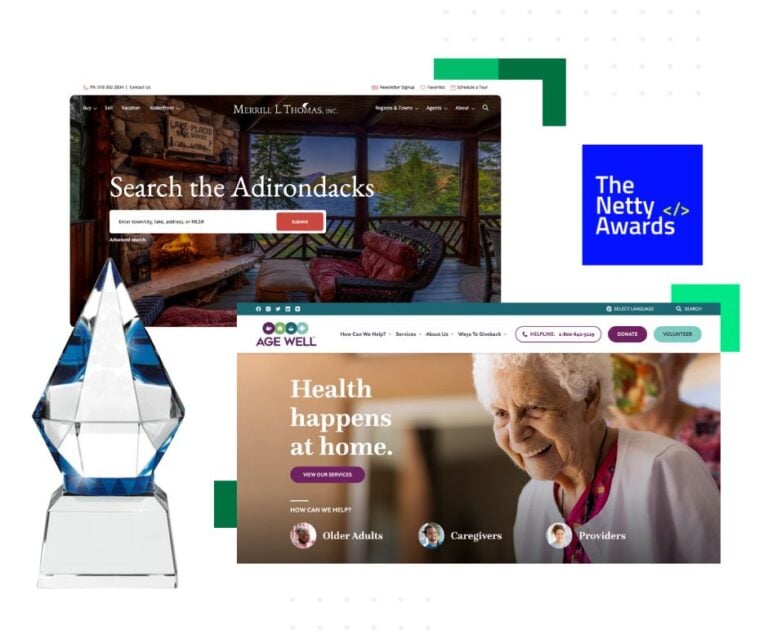
Bytes.co Celebrates Double Victory at 2023 Netty Awards

Bytes.co Shines at the 2023 w3 Awards

Bytes.co Triumphs at the 2023 Davey Awards
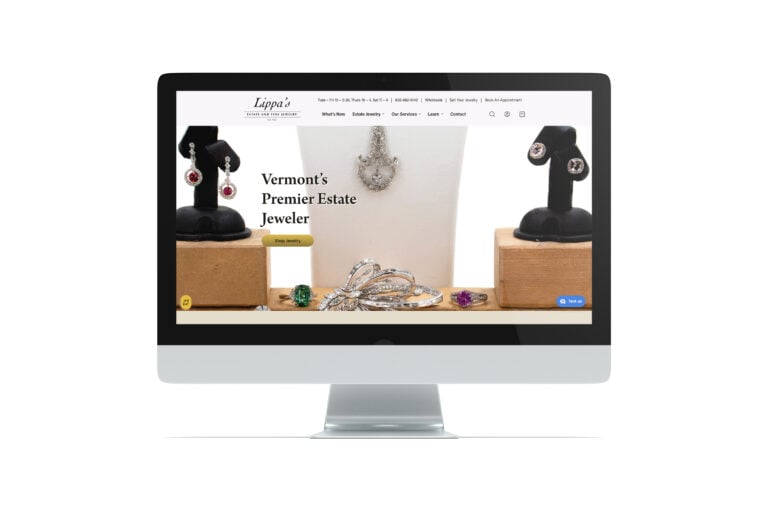
Lippa’s Estate & Fine Jewelry Website Launch

Davis & Hodgdon Advisory Group and Copper Leaf Financial Dual Website Launch
